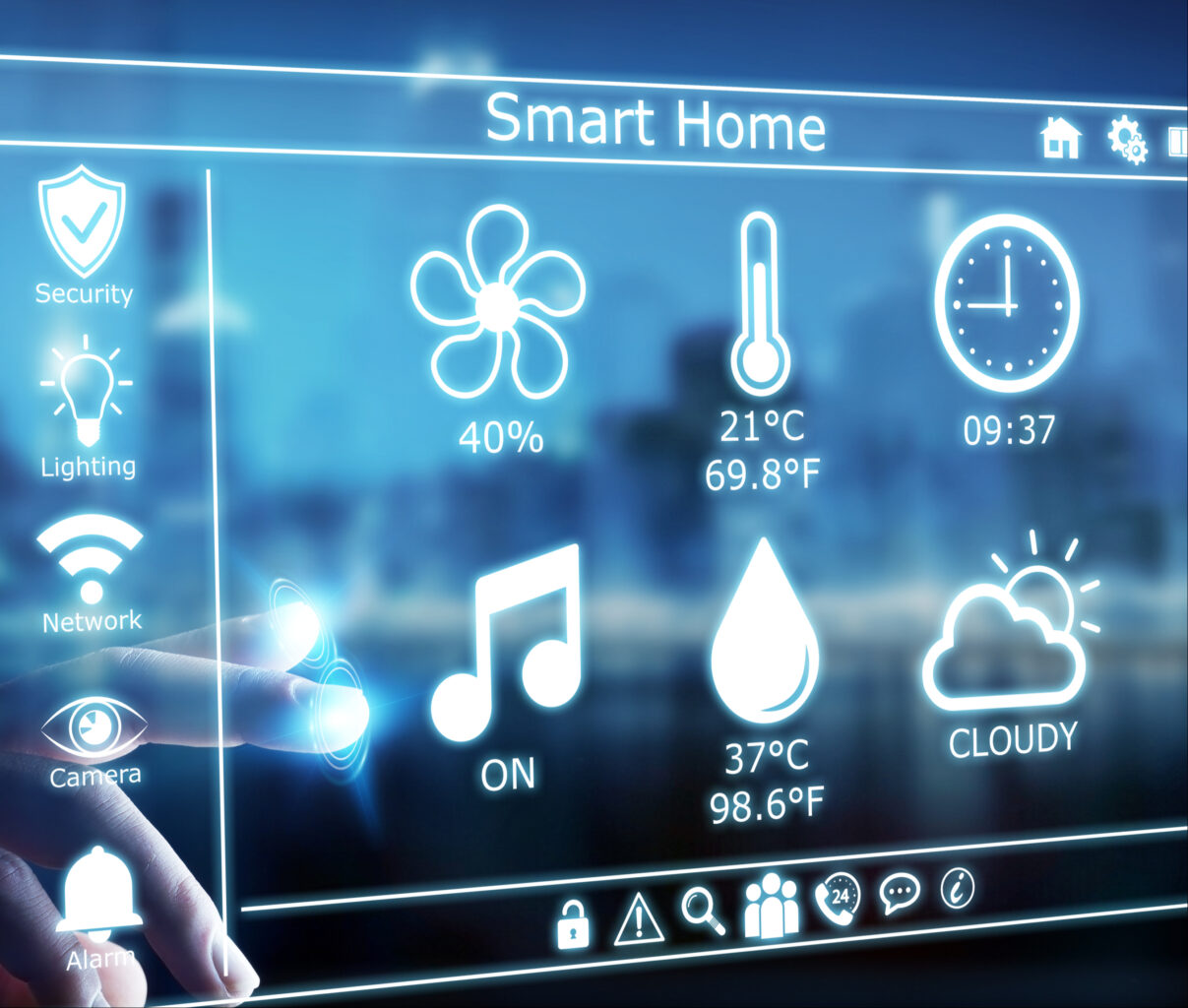
In the past few decades, electronic devices in our homes have transformed from ordinary objects into what was only thought possible in science fiction movies. Televisions, refrigerators, security cameras, speakers, among others, have been fitted with sensors that allow them to see, touch, and hear their surroundings, as they can transform physical data into digital data. When brought together, these devices make up smart homes or in most cases, “internet of things”.
Just about every device with network connectivity is initiated to the internet of things. In smart homes, these gadgets relieve us from chores, allowing us to have a breather, while adding magic to ordinary experiences. If you are yet to delve into this world, you might be lost on where to start. Lucky for you, we have just the right devices that will set your home on the path to being a smart home.
We have a list of the most common devices that cut across all smart homes. These include smart speakers that you can converse with, smart security devices that will amp the security in your home and smart controls that allow you to orchestrate things in your home regardless of your physical presence. Are you hooked? Buckle up as we start off with smart speakers.
Amazon Echo vs Sonos One
Amazon Echo
Amazon’s Echo smart speaker first came into the market in 2015 and has maintained the lead in the smart devices market. The Amazon Echo is a series of smart speakers and mobile accessories that are internet-connected and are paired with Alexa, Amazon’s digital assistant. It wears different hats including serving as an IoT hub, internet search engine, a music player, and pretty much anything that Alexa Skill allows it to do. Let’s take a look at Amazon’s 2020 Echo.
Being a smart speaker, its primary purpose is offering sound and compared to former Echo products in the past, the Amazon 2020 Echo has improved sound quality. For starters, this smart speaker has adaptive sound, enabling it to adjust to a room’s acoustics. Also, it’s 3-inch woofer and dual 0.8-inch tweeters, lower-range mids and bass are stronger and richer. Additionally, it boasts of power, that is, more volume.
In addition to offering sound, the Amazon Echo is an integral smart home hardware. This particular speaker has two ways that smart home devices can connect to it. One, the Zigbee receiver allows the Echo to connect with other smart home devices, without an additional hub. With this receiver, Echo users are able to hook a wide range of gadgets in their house without having to worry about a smart home hub. Two, the Amazon Sidewalk aims at creating a shared network that will benefit any Sidewalk-enabled devices that are in a community.
Pros
- Has improved sound quality and more bass
- Improved smart home connectivity
- Hassle-free stereo pairing
Cons
- Has a bulky design
Sonos One
When it hit the market, the Sonos One brought a revolution. It was among the first smart speakers that didn’t have users choosing between excellent sound quality and smarts because it had both. It also didn’t have users choosing between Google Assistant and Alexa.
The top of the smart speaker has a touch-sensitive surface. Swiping right or left will skip forward or backwards in your playlist. Tapping in the surface’s center pauses and plays your music. Finally, when you tap the right and left halves of the panel, you raise or lower the volume. However, you’ll probably spend most of your time controlling the Sonos using the app. The device also boasts of voice control where the speaker has six internal microphones that enable it to hear your instructions, and a pair of Class-D amplifiers as well as a tweeter / mid-woofer driver combination.
Setting up the Sonos involves installing both the Sonos and Alexa apps, signing into both your Sonos and Amazon accounts, and any music streaming services that you might want to listen to using the speaker. The speaker encourages you to perform a ‘Trueplay Tuning’ process, where you move around the room with your phone while your speaker plays some test sounds. Your phone then establishes how your speaker sounds while in the environment, and tunes its sound.
Pros
- Is the best Alexa and Google Assistant speaker
- Has a great app and supports many streaming services
Cons
- Does not use Bluetooth
Final Verdict
The Sonos One is better overall because it is a compact smart speaker with a great app, support for multiple streaming services and digital assistants. However, in bigger rooms, the Amazon Echo Studio produces a huge sound. It also boasts of more features than the Sonos One, including its sensitive microphones that allow Alexa to hear you over loud music.
When it comes to features, Echo Studio boasts of more features including being able to connect to a TV while also being able to replay Dolby Atmos streams. The Sonos One advantage over the Echo is that you can use either Amazon Alexa or Google Assistant to control it.
Smart Home Security Systems: SimpliSafe vs Cove
With the evolution of smart homes, home security had to be featured. The thing is, home security cannot be confined to one gadget but instead comes as a package. These include security systems that can be paired with Google Assistant or Alexa and that you can install on your own or have it down professionally. First off is Simplisafe.
Simplisafe
Simplisafe is the most popular choice of home security systems that are no-contract, easy to set up and quite affordable. In an hour’s time, you’ll be able to set up environmental and security protection. Additionally, you can have it professionally monitored for $14.99 a month. However, DIY monitoring is also available through the Simplisafe mobile app.
The SimpliSafe starter set includes a base station, a wireless keypad, a keyring remote, one motion and two entry sensors. All these are at a starter set cost of $244. The deal also includes a SimpliCam, a high def video security camera that has a motion sensor and sends alerts.
SimpliSafe’s equipment is inexpensive but very high quality. For example, they have SmashSafe, a backup against tampering. If someone attempts to disable their system, their monitoring services alerts the police. They also boast of a Heartbeat feature, which checks continuously that the security system is working.
Setting up the system is quite easy. In fact, most customers do it on their own with only about three percent asking for assistance. All equipment is either freestanding or can be attached to surfaces using removable adhesive.
Pros
- There are no long-term contracts to sign
- Easy to install
- Affordable monitoring plans
- Professional monitoring
Cons
- Costly up-front equipment costs
- Too simple for some homes
Cove
If you’re looking for a quick yet easy setup, then Cove is the system for you. You save money by installing the system on your own. The system is already pre-programmed even before it is shipped. All you have to do is to stick the sensors to your walls using their 3M-backed adhesives.
All of Cove’s systems call for 24/7 professional monitoring, but you can either sign up for a month if you paid for the equipment upfront, or sign up for three years if you don’t want to pay for the equipment upfront.
During emergencies, Cove’s team texts you, which comes in handy if you should ever find yourself in a hostage situation. This explains why Cove’s response rate is 10x faster than competitors.
Pros
- Can be integrated with Google Assistant and Alexa
- You can choose to pay nothing upfront
- Has battery backup
Cons
- Professional monitoring a must
- Expensive remote control
Final Verdict
The Simplisafe Security System is better overall because it has an option for no contract making it easy and affordable to install in your home. Additionally, their equipment is inexpensive because they make it on their own and there are no middlemen involved. However, being able to integrate digital assistants gives Cove an advantage over SimpliSafe. However, both are quite inexpensive and easy to install.
Smart Home Controls: Amazon Echo (4th gen) vs Samsung SmartThings Hub v3
If the smart home devices in your home are to ‘talk’ to each other, you’ll need a smart home control or smart home hub. This is the gadget that brings together all your devices and allows you to control them using one app. With that said, let’s take a look at two of the best smart home controls currently.
Amazon Echo (4th gen)
In site of this gadget having featured in the smart speakers spot, it also makes for a great smart home control. The combination of Bluetooth, Wi-Fi, and Zigbee make the Echo the best smart home control for most people. Furthermore, it has multiple radios, which help connect with a large number of low-power smart home devices. With Alexa’s routines, you’ll be able to use a number of triggers to activate other smart home devices.
The hub also collaborates with Alexa Guard, which listens to smoke alarms and glass breaking, and can notify you in case of an emergency. Finally, it supports Amazon Sidewalk, which works with such things as Tile trackers and smart lights especially over greater distances.
Pros
- Awesome smart home skills
- Impeccable spherical design
- Good audio
Cons
- No battery backup
Samsung SmartThings Hub v3
This smart home hub is a darling among critics because it supports both Zigbee and Z-Wave. This allows you to link to hundreds of devices, which is considerably more than most hubs. Additionally, the SmartThings app is full of functionality, which allows you to come up with a diverse range of different scenarios for all gadgets in your home.
This SmartHub also boasts of in-built Wi-Fi, meaning you don’t have to plug the device into your router. This gives you the freedom to place the smart home control in a location that is most convenient to you connecting it with other smart home devices.
The downside is that it doesn’t have battery backup. Then again, if the lights go out, chances are you won’t be needing to turn your lights on.
Pros
- Supports Wi-Fi which makes installing easy
- Supports automation more than any other hubs
- Works with Z-Wave and Zigbee devices
Cons
- Doesn’t work with Nest products at the moment
Final Verdict
The Amazon Echo is the favorite for most people because of it’s ability to connect with many low-power smart home devices, thanks to its many radios. However, SmartThings ability to work with Z-Wave and Zigbee devices gives it somewhat of an advantage too. The Amazon Echo also boasts of better audio quality, especially at its price. The voice assistant, Alexa, is also pretty advanced which makes the smart hub, a darling to many.
Conclusion
The Internet of Things or smart homes are not in the future, they are here, and here to stay. In 2018, there were about 23 billion devices that were connected. Forecasters believe that the number will climb to more than 75 billion in 2025. This is mostly because people are becoming more comfortable with having these devices sit in their living room. Also, tech companies are dreaming up of new devices each day that work towards making life more comfortable.
The future is evident in the evolution that is smart offices, smart buildings and even smart cities. Companies like Google are working towards autonomous vehicles that will connect to the internet and drive themselves to the destination of your choice. The bottomline is, smart devices are here to stay.
The above smart devices are a good place to start when looking to transform your home into a smart home. Smart speakers and smart controls will be the heartbeat of every smart phone and purchasing one now is giving yourself a head start. Smart security systems also offer a cheap yet reliable way to ensure homes are safe. The fact that you can check up on your home remotely also makes them an attractive option. However, do your research before making a purchase depending on your needs.